session hijacking smart card cac I went over to theirs and inserted my CAC using a 2nd CAC reader. I digitally signed the PDF then went back over to my computer. Trying to log-in I got the message "This CAC is blocked". The second way to use NFC tags is to encode an NDEF message to the tag, (again you can use the NFC app to do this) that triggers a Shortcut directly - no automation needed. In the NFC app go to "Write" and click on the little "+" in .
0 · When Your Smart ID Card Reader Comes With Malware
1 · Smart Card Reader not detected on remote host using Remote
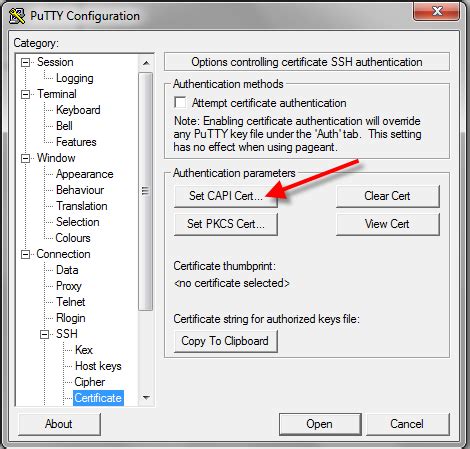
2 · Smart Card Reader (CAC) operation
3 · Smart Card Logon for SSH
4 · Session Hijacking 2.0 — The Latest Way That Attackers are
5 · Session Hijacking
6 · MilitaryCAC's Help Installing drivers / Firmware update / check
7 · MilitaryCAC's Common Problems and Solutions for CAC Installation
8 · CAC getting randomly "blocked"? : r/AirForce
9 · Attacking RDP from Inside: How we abused named pipes for
Yes they should work, for Skylanders you need cards that are: 1k, 13.56MHz, uid/block 0 writeable. If they don't say 1k, but S50 they are 1k too. You'd also preferably use an acr122u as it's the most used by the skylander community to make make Skylanders with NFC cards. If you ever need help, feel free to join this discord server . There is a .
Is there a physical "CardPresent" switch or is it the physical contacts to the chip on the card that provides continuous authorization? Or is it both? In other words, once a card is . Solution 1-2: If you have an SCR-331 CAC Reader and using Vista, Windows 7, or 8, and are still having problems getting the reader to be recognized by ActivClient, or your . You can do this by opening the Device Manager on the remote machine and checking if the smart card reader is listed under "Smart card readers". If it is not listed, you .I went over to theirs and inserted my CAC using a 2nd CAC reader. I digitally signed the PDF then went back over to my computer. Trying to log-in I got the message "This CAC is blocked".
To hijack a session, you need to first steal the session cookies associated with a live user session. In the modern sense, there are two main approaches to this: Using modern . Malicious firmware in a smart card reader can also try to steal your PIN, or cause a DOS attack by locking the card with multiple PIN failures.Click Session and enter a remote server’s hostname or IP address. For Connection type, click SSH. (Notice that under Port, 22 appears.) Enter a session name in Saved Sessions and click . Try this first: Go to Device Manager (Instructions are above), scroll down to Smart Card readers, right click the CAC reader that shows up below Smart Card Readers. It can also .
The Grand Finale: Hijacking Smart Cards. Smart card redirection also uses the RDPDR channel; it is just another device. This means that if a user connects using a smart . The web server sends the token to the client browser after the client has been authenticated. Through session hijacking, attackers can intercept, predict, or brute-force a . Is there a physical "CardPresent" switch or is it the physical contacts to the chip on the card that provides continuous authorization? Or is it both? In other words, once a card is inserted and the computer reads the chip and authorizes access, what is the mechanism that de-authorizes the session?
Solution 1-2: If you have an SCR-331 CAC Reader and using Vista, Windows 7, or 8, and are still having problems getting the reader to be recognized by ActivClient, or your CAC reader shows up as STCII Smart Card Reader follow . You can do this by opening the Device Manager on the remote machine and checking if the smart card reader is listed under "Smart card readers". If it is not listed, you may want to check if the smart card reader driver is installed on the remote machine. I went over to theirs and inserted my CAC using a 2nd CAC reader. I digitally signed the PDF then went back over to my computer. Trying to log-in I got the message "This CAC is blocked".
To hijack a session, you need to first steal the session cookies associated with a live user session. In the modern sense, there are two main approaches to this: Using modern phishing toolkits such as AitM and BitM. Using tools that target browser data such as infostealers. Malicious firmware in a smart card reader can also try to steal your PIN, or cause a DOS attack by locking the card with multiple PIN failures.Click Session and enter a remote server’s hostname or IP address. For Connection type, click SSH. (Notice that under Port, 22 appears.) Enter a session name in Saved Sessions and click Save. Once you have an account, open PuTTY-CAC and insert your PIV/CAC card into your card reader. Click a Saved Session and Load. Try this first: Go to Device Manager (Instructions are above), scroll down to Smart Card readers, right click the CAC reader that shows up below Smart Card Readers. It can also show up under unknown devices.

When Your Smart ID Card Reader Comes With Malware
The Grand Finale: Hijacking Smart Cards. Smart card redirection also uses the RDPDR channel; it is just another device. This means that if a user connects using a smart card (or just redirects their smart card to use it from within the session), the attacker could also take over the user’s smart card and use it as if it were connected to . The web server sends the token to the client browser after the client has been authenticated. Through session hijacking, attackers can intercept, predict, or brute-force a legitimate session token in order to pose as the authenticated . Is there a physical "CardPresent" switch or is it the physical contacts to the chip on the card that provides continuous authorization? Or is it both? In other words, once a card is inserted and the computer reads the chip and authorizes access, what is the mechanism that de-authorizes the session? Solution 1-2: If you have an SCR-331 CAC Reader and using Vista, Windows 7, or 8, and are still having problems getting the reader to be recognized by ActivClient, or your CAC reader shows up as STCII Smart Card Reader follow .
You can do this by opening the Device Manager on the remote machine and checking if the smart card reader is listed under "Smart card readers". If it is not listed, you may want to check if the smart card reader driver is installed on the remote machine.
I went over to theirs and inserted my CAC using a 2nd CAC reader. I digitally signed the PDF then went back over to my computer. Trying to log-in I got the message "This CAC is blocked".
To hijack a session, you need to first steal the session cookies associated with a live user session. In the modern sense, there are two main approaches to this: Using modern phishing toolkits such as AitM and BitM. Using tools that target browser data such as infostealers. Malicious firmware in a smart card reader can also try to steal your PIN, or cause a DOS attack by locking the card with multiple PIN failures.
Click Session and enter a remote server’s hostname or IP address. For Connection type, click SSH. (Notice that under Port, 22 appears.) Enter a session name in Saved Sessions and click Save. Once you have an account, open PuTTY-CAC and insert your PIV/CAC card into your card reader. Click a Saved Session and Load. Try this first: Go to Device Manager (Instructions are above), scroll down to Smart Card readers, right click the CAC reader that shows up below Smart Card Readers. It can also show up under unknown devices.
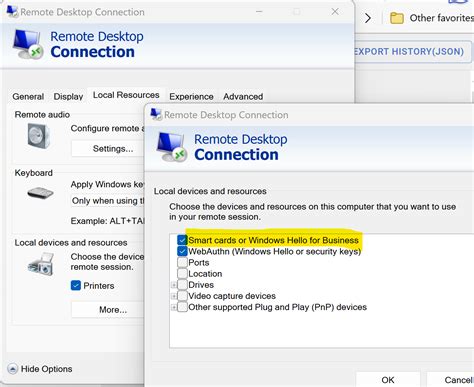
The Grand Finale: Hijacking Smart Cards. Smart card redirection also uses the RDPDR channel; it is just another device. This means that if a user connects using a smart card (or just redirects their smart card to use it from within the session), the attacker could also take over the user’s smart card and use it as if it were connected to .
 operation .jpg)
what are the cowboys standings
Smart Card Reader not detected on remote host using Remote
HiHello is the best digital business card app and has a built-in NFC tag reader, so you can have all the benefits of a digital card and have the ability to share your card using NFC. The best part is that, unlike other NFC business card apps that charge you a premium for their NFC hardware, HiHello is free to use—you’ll just need to .
session hijacking smart card cac|MilitaryCAC's Help Installing drivers / Firmware update / check