use of a smart card for authentication Smart cards are tamper-resistant portable storage devices that can enhance the security of tasks such as authenticating clients, signing code, securing e-mail, and signing in .
Here are some of my favorite creative ways to use NFC tags with your iPhone. 1. Instantly connect to a Wi-Fi network. One of the biggest pains of living in the digital age is remembering complicated passwords. NFC can .What is the ST25DV-I2C series? These NFC Forum Type 5 Dynamic tags operate in the high-frequency range (13.56 MHz). The data stored in tags can be accessed by any NFC smartphone or NFC/RFID HF professional reader, and .
0 · smart card multi factor authentication
1 · smart card identity
2 · smart card based identification system
3 · smart card authentication step by
4 · smart card authentication protocol
5 · enable smart card log on
6 · enable smart card authentication
7 · authenticate using your smart card
Hi everyone, I'm looking for some instruction on how to set up a clock in/out and break system .
Smart cards let you use extra checks too, like a code or your body, to make authentication even safer. Smart cards use complex codes to keep data safe and stop .How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system. Smart cards let you use extra checks too, like a code or your body, to make authentication even safer. Smart cards use complex codes to keep data safe and stop . For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential .
Smart Card Authentication is a means of verifying users into enterprise resources such as workstations and applications using a physical card in tandem with a smart card reader and .
Smart cards are tamper-resistant portable storage devices that can enhance the security of tasks such as authenticating clients, signing code, securing e-mail, and signing in . Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, .
rfid protection sleeve for credit card
Smart card authentication requires two things: the smart card itself and a pin entered by the user. With smart cards there are two different ways to authenticate yourself into a system, there is .
Smart card authentication is an important part of cybersecurity, providing an extra layer of protection in our increasingly digital world. It involves the use of smart cards, which are small, . Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data .A smart card is a secure microcontroller that is typically used for generating, storing and operating on cryptographic keys. Smart card authentication provides users with smart card devices for .
How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system.
Smart cards let you use extra checks too, like a code or your body, to make authentication even safer. Smart cards use complex codes to keep data safe and stop . For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential .Smart Card Authentication is a means of verifying users into enterprise resources such as workstations and applications using a physical card in tandem with a smart card reader and . Smart cards are tamper-resistant portable storage devices that can enhance the security of tasks such as authenticating clients, signing code, securing e-mail, and signing in .
Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, .Smart card authentication requires two things: the smart card itself and a pin entered by the user. With smart cards there are two different ways to authenticate yourself into a system, there is .
Smart card authentication is an important part of cybersecurity, providing an extra layer of protection in our increasingly digital world. It involves the use of smart cards, which are small, . Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data .
rfid pvc sticker
rfid rc522 read tag
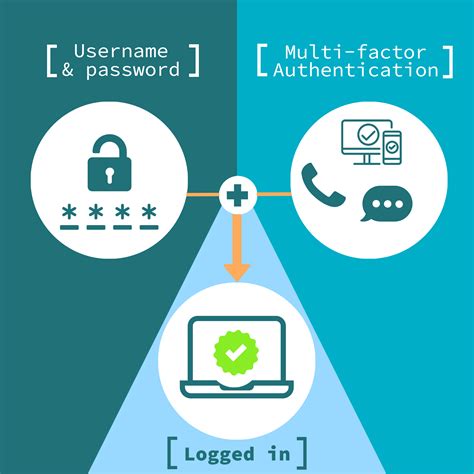
smart card multi factor authentication
Listen online to ESPN 106.7 radio station for free – great choice for Auburn, United States. Listen live ESPN 106.7 radio with Onlineradiobox.com . Opelika, with the call-sign WGZZ-HD3, is a sports-format radio station serving Auburn .You can listen to live Auburn Tigers games online or on the radio dial. With 54 stations in the network, the Auburn Sports Network represents one of the biggest and most-listened to college sports network in the South. All home and away .
use of a smart card for authentication|smart card identity