smart cards use eap EAP is used on encrypted networks to provide a secure way to send identifying information to . Get the best deals for Fierce Deity Link Botw at eBay.com. We have a great .
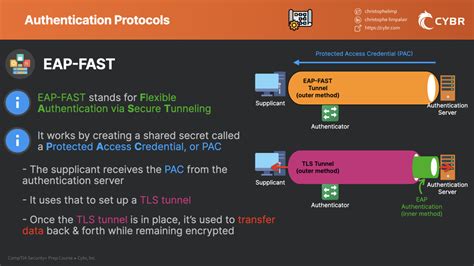
0 · what is eap fast
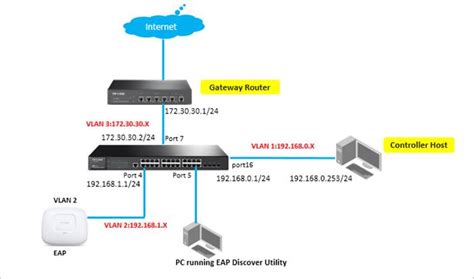
1 · network access eap
2 · eap sim codes
3 · eap sim
4 · eap network access examples
5 · eap for windows 10
6 · eap authentication protocol examples
7 · 3gpp eap
Order cards in bulk. You can order fares of $25 or more in advance by using our Group Orders program. You can purchase 1-way or round trip bus and subway fares, 1- or 7-day passes, or monthly passes for the bus and subway system. .
EAP is used on encrypted networks to provide a secure way to send identifying information to .
access control card reader hs code
It’s compatible with several authentication methods, such as public key encryption, smart cards, certificates, token cards, and one-time passwords. . By default, two EAP types are available, Secured password (EAP-MSCHAPv2) .This article contains configuration information specific to the following authentication methods in EAP. EAP-Transport Layer Security (EAP-TLS): Standards-based EAP method that uses TLS with certificates for mutual authentication. Appears .
what is eap fast
EAP is used on encrypted networks to provide a secure way to send identifying information to provide network authentication. It supports various authentication methods, including as token cards, smart cards, certificates, one-time passwords and public key encryption.It’s compatible with several authentication methods, such as public key encryption, smart cards, certificates, token cards, and one-time passwords. EAP protocol safeguards a particular portal, limiting network access to only those with an authentication key or password.
By default, two EAP types are available, Secured password (EAP-MSCHAPv2) and Smart card or other certificate (EAP-TLS). However, EAP is a flexible protocol that allows inclusion of additional EAP methods, and it is not restricted to these two types. EAP ideally works on encrypted networks to transmit identifying information required for network authentication. Experts consider it a framework because it offers a range of authentication mechanisms for OTPs, token cards, digital certificates, smart cards, and public-key encryption authentication. When you use EAP with a strong EAP type, such as TLS with smart cards, or TLS with certificates, both the client and the server use certificates to verify identities to each other. Certificates must meet specific requirements both on the .EAP provides authentication methods that use security devices, such as smart cards, token cards, and crypto calculators. EAP provides an industry-standard architecture for supporting additional authentication methods within PPP.
network access eap
eap sim codes
802.1X uses EAP on encrypted point-to-point networks to send information between a supplicant and authentication server. Unlike other authentication protocols in which a client requests authentication, EAP is designed so the authenticator initiates the request to grant access to a client.

The EAP methods (EAP-type) are located in the smart card and may be implemented as a client application. The EAP methods are responsible for the smart card’s own authentication algorithms, as well as for fragmentation and reassembly in accordance with the physical communication interface.
This flexibility enables EAP to support different authentication mechanisms, such as passwords, digital certificates, smart cards, token-based authentication, biometrics, and more. The EAP framework consists of three main components: the EAP peer, the .
This article contains configuration information specific to the following authentication methods in EAP. EAP-Transport Layer Security (EAP-TLS): Standards-based EAP method that uses TLS with certificates for mutual authentication. Appears .EAP is used on encrypted networks to provide a secure way to send identifying information to provide network authentication. It supports various authentication methods, including as token cards, smart cards, certificates, one-time passwords and public key encryption.It’s compatible with several authentication methods, such as public key encryption, smart cards, certificates, token cards, and one-time passwords. EAP protocol safeguards a particular portal, limiting network access to only those with an authentication key or password. By default, two EAP types are available, Secured password (EAP-MSCHAPv2) and Smart card or other certificate (EAP-TLS). However, EAP is a flexible protocol that allows inclusion of additional EAP methods, and it is not restricted to these two types.
EAP ideally works on encrypted networks to transmit identifying information required for network authentication. Experts consider it a framework because it offers a range of authentication mechanisms for OTPs, token cards, digital certificates, smart cards, and public-key encryption authentication. When you use EAP with a strong EAP type, such as TLS with smart cards, or TLS with certificates, both the client and the server use certificates to verify identities to each other. Certificates must meet specific requirements both on the .
EAP provides authentication methods that use security devices, such as smart cards, token cards, and crypto calculators. EAP provides an industry-standard architecture for supporting additional authentication methods within PPP. 802.1X uses EAP on encrypted point-to-point networks to send information between a supplicant and authentication server. Unlike other authentication protocols in which a client requests authentication, EAP is designed so the authenticator initiates the request to grant access to a client.
The EAP methods (EAP-type) are located in the smart card and may be implemented as a client application. The EAP methods are responsible for the smart card’s own authentication algorithms, as well as for fragmentation and reassembly in accordance with the physical communication interface.
eap sim
eap network access examples
Google Kenya and Equity Bank today launched BebaPay, an NFC enabled electronic payment card and app in a move they say will make .
smart cards use eap|3gpp eap