pki smart card wiki PKI provides "trust services" - in plain terms trusting the actions or outputs of entities, be they people or computers. Trust service . See more Proceed as follows: First open the Settings app on your iPhone. Then select the option “Control Center”. Scroll down and tap the green plus button to the left of “NFC Tag Reader”. The .
0 · smart card two factor authentication
1 · smart card computer access
2 · smart card authentication step by
3 · pki smarttoken
4 · pki smart card authentication
5 · fips 140 2 smart card
6 · authentication smart card
7 · adfs smart card authentication
Auburn's first, Auburn's best, and Auburn's favorite Sports Call-in radio program. Broadcasting LIVE from Auburn's own Tiger 93.9 FM.
smart card two factor authentication
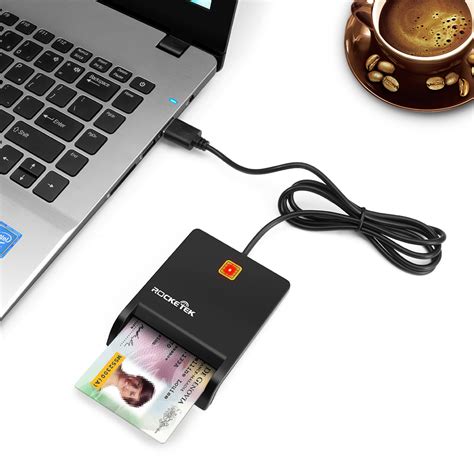
usb rfid card reader
smart card computer access
A public key infrastructure (PKI) is a set of roles, policies, hardware, software and procedures needed to create, manage, distribute, use, store and revoke digital certificates and manage public-key encryption. The purpose of a PKI is to facilitate the secure electronic transfer of information for a range of network . See morePKI provides "trust services" - in plain terms trusting the actions or outputs of entities, be they people or computers. Trust service . See morePublic-key cryptography is a cryptographic technique that enables entities to securely communicate on an insecure public network, and reliably . See more
Developments in PKI occurred in the early 1970s at the British intelligence agency GCHQ, where James Ellis, Clifford Cocks and others made important discoveries related to encryption . See more• OpenSSL is the simplest form of CA and tool for PKI. It is a toolkit, developed in C, that is included in all major Linux distributions, and can . See moreCertificate authoritiesThe primary role of the CA is to digitally sign and publish the public key bound to a given user. This is . See more

PKIs of one type or another, and from any of several vendors, have many uses, including providing public keys and bindings to user identities which are used for: See moreSome argue that purchasing certificates for securing websites by SSL/TLS and securing software by code signing is a costly venture for . See more
zebra fixed rfid reader
Smart cards serve as credit or ATM cards, fuel cards, mobile phone SIMs, authorization cards for pay television, household utility pre-payment cards, high-security identification and access badges, and public transport and public phone payment cards. Smart cards may also be used as electronic wallets. The smart card chip can .This Personal Identity Verification (PIV) 101 is intended to help you understand the purpose and uses of a PIV credential at your organization. This PIV 101 focuses on using PIV credentials .A public key infrastructure (PKI) is a set of roles, policies, hardware, software and procedures needed to create, manage, distribute, use, store and revoke digital certificates and manage public-key encryption.Smart cards serve as credit or ATM cards, fuel cards, mobile phone SIMs, authorization cards for pay television, household utility pre-payment cards, high-security identification and access badges, and public transport and public phone payment cards.
PKI, or public key infrastructure, encompasses everything used to establish and manage public key encryption. This includes software, hardware, policies, and procedures that are used to create, distribute, manage, store, and revoke digital certificates.This Personal Identity Verification (PIV) 101 is intended to help you understand the purpose and uses of a PIV credential at your organization. This PIV 101 focuses on using PIV credentials for logical access such as authenticating to networks or .Introduction. Public Key Infrastructure or PKI is a cost effective tool to ensure the confidentiality, integrity, and availability of electronic transactions. PKI utilizes asymmetric cryptography, meaning a different key is used to encrypt (public key) than is used to decrypt (private key).
OpenSC provides a set of libraries and utilities to work with smart cards. Its main focus is on cards that support cryptographic operations, and facilitate their use in security applications such as authentication, mail encryption and digital signatures.
What Is the Federal PKI? The Federal PKI is a network of certification authorities (CAs) that issue: PIV credentials and person identity certificates. PIV-Interoperable credentials and person identity certificates. Other person certificates. A small number of .
The public key encrypts data, and. The private key decrypts it. For you skimmers, here’s a quick overview of PKI basics in video form: What is Public Key Infrastructure (PKI) by Securemetric. Watch on. Up until the 1970s, encryption was always symmetric, meaning that one key would encrypt and decrypt data.
Edward Robin. September 17, 2023. Data Security. Public Key Infrastructure (PKI) and Smart Cards are cornerstones of digital security. We will look into how PKI works with smart cards and their role in ensuring secure data transmission. In this Article: Understanding Public Key Infrastructure (PKI)
Aventra MyEID PKI Card is a cryptographic smart card conforming to common Public Key Infrastructure standards like ISO7816 and PKCS#15. It can be used for various tasks requiring strong cryptography, e. g. logging securely to Windows, encrypting e-mail, authentication, and electronic signatures.A public key infrastructure (PKI) is a set of roles, policies, hardware, software and procedures needed to create, manage, distribute, use, store and revoke digital certificates and manage public-key encryption.Smart cards serve as credit or ATM cards, fuel cards, mobile phone SIMs, authorization cards for pay television, household utility pre-payment cards, high-security identification and access badges, and public transport and public phone payment cards. PKI, or public key infrastructure, encompasses everything used to establish and manage public key encryption. This includes software, hardware, policies, and procedures that are used to create, distribute, manage, store, and revoke digital certificates.
This Personal Identity Verification (PIV) 101 is intended to help you understand the purpose and uses of a PIV credential at your organization. This PIV 101 focuses on using PIV credentials for logical access such as authenticating to networks or .
Introduction. Public Key Infrastructure or PKI is a cost effective tool to ensure the confidentiality, integrity, and availability of electronic transactions. PKI utilizes asymmetric cryptography, meaning a different key is used to encrypt (public key) than is used to decrypt (private key). OpenSC provides a set of libraries and utilities to work with smart cards. Its main focus is on cards that support cryptographic operations, and facilitate their use in security applications such as authentication, mail encryption and digital signatures.What Is the Federal PKI? The Federal PKI is a network of certification authorities (CAs) that issue: PIV credentials and person identity certificates. PIV-Interoperable credentials and person identity certificates. Other person certificates. A small number of .
The public key encrypts data, and. The private key decrypts it. For you skimmers, here’s a quick overview of PKI basics in video form: What is Public Key Infrastructure (PKI) by Securemetric. Watch on. Up until the 1970s, encryption was always symmetric, meaning that one key would encrypt and decrypt data.Edward Robin. September 17, 2023. Data Security. Public Key Infrastructure (PKI) and Smart Cards are cornerstones of digital security. We will look into how PKI works with smart cards and their role in ensuring secure data transmission. In this Article: Understanding Public Key Infrastructure (PKI)

A Lenovo ThinkPad X240. From what I remember, integrated NFC readers built into many laptops and tablets typically are not PC/SC enabled.
pki smart card wiki|adfs smart card authentication