windows 7 smart card encryption You can use smart card certificates with BitLocker Drive Encryption to protect fixed and removable data drives and to recover BitLocker-protected drives in the absence of the primary access key. Once you have obtained certificates, you can use them with BitLocker data recovery agents and as a BitLocker key protector for data drives. There are a number of easy ways to pay your Koodo bill from paying directly .
0 · Understanding and Evaluating Virtual Smart Cards
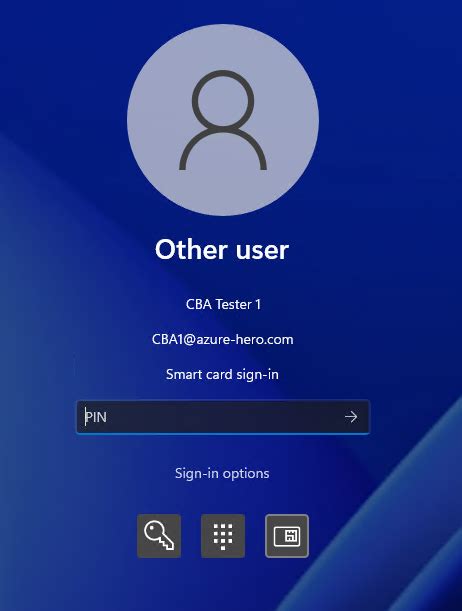
1 · How Smart Card Sign
2 · Encrypt Drives with BitLocker To Go
NFL top-10 rankings: Chiefs top Lions; Steelers, Bills, Eagles climb; Falcons drop out. Check out our guide to the 2024-25 NFL Playoffs including the current bracket and playoff .
How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to . Virtual smart cards that utilize a TPM provide the three main security principles of traditional smart cards: nonexportability, isolated cryptography, and anti-hammering. Virtual smart cards are less expensive to implement and more convenient for users.How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system. Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers.
You can use smart card certificates with BitLocker Drive Encryption to protect fixed and removable data drives and to recover BitLocker-protected drives in the absence of the primary access key. Once you have obtained certificates, you can use them with BitLocker data recovery agents and as a BitLocker key protector for data drives. First of all not every smart card can be used for Windows 7 logon. You need a smart card that is supported by Windows 7 or that activates support by installing a certain smart card management component. Encrypting and Decrypting Files with Smartcards and PowerShell. Tim's Blog. 2018-09-28. So you want to send a file securely to someone using their smart card certificate, but without using S/MIME? PowerShell can come to the rescue.Brandon Lee Mon, Aug 2 2021 encryption, security 1. Virtual smart cards provide the benefits of physical smart cards without extra costs or hardware. They are based on a Trusted Platform Module (TPM) and authenticate users with a certificate against Active Directory, like a physical smart card. Author. Recent Posts.
Feature description. Virtual smart card technology offers comparable security benefits to physical smart cards by using two-factor authentication. Virtual smart cards emulate the functionality of physical smart cards, but they use the Trusted Platform Module (TPM) .1 Answer. Sorted by: 3. Many of the requirements are listed in this KB article http://support.microsoft.com/kb/281245. The smart card certificate has specific format requirements: The CRL Distribution Point (CDP) location (where CRL is the Certification Revocation List) must be populated, online, and available. For example:Smart card: To use a smart card with BitLocker, you must have a compatible certificate on your smart card. BitLocker will automatically choose the certificate unless you have multiple compatible certificates, in which case you must choose the certificate to use.
Virtual smart cards that utilize a TPM provide the three main security principles of traditional smart cards: nonexportability, isolated cryptography, and anti-hammering. Virtual smart cards are less expensive to implement and more convenient for users.How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system. Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers.
You can use smart card certificates with BitLocker Drive Encryption to protect fixed and removable data drives and to recover BitLocker-protected drives in the absence of the primary access key. Once you have obtained certificates, you can use them with BitLocker data recovery agents and as a BitLocker key protector for data drives. First of all not every smart card can be used for Windows 7 logon. You need a smart card that is supported by Windows 7 or that activates support by installing a certain smart card management component. Encrypting and Decrypting Files with Smartcards and PowerShell. Tim's Blog. 2018-09-28. So you want to send a file securely to someone using their smart card certificate, but without using S/MIME? PowerShell can come to the rescue.Brandon Lee Mon, Aug 2 2021 encryption, security 1. Virtual smart cards provide the benefits of physical smart cards without extra costs or hardware. They are based on a Trusted Platform Module (TPM) and authenticate users with a certificate against Active Directory, like a physical smart card. Author. Recent Posts.

Understanding and Evaluating Virtual Smart Cards
Feature description. Virtual smart card technology offers comparable security benefits to physical smart cards by using two-factor authentication. Virtual smart cards emulate the functionality of physical smart cards, but they use the Trusted Platform Module (TPM) .1 Answer. Sorted by: 3. Many of the requirements are listed in this KB article http://support.microsoft.com/kb/281245. The smart card certificate has specific format requirements: The CRL Distribution Point (CDP) location (where CRL is the Certification Revocation List) must be populated, online, and available. For example:

will rfid read thru plastic
How Smart Card Sign
Best contactless cards. Best for groceries: Blue Cash Preferred® Card from American Express. Best for food delivery: American Express® Gold Card. Best for 0% APR: Citi Simplicity® Card. Best .
windows 7 smart card encryption|How Smart Card Sign