secure rfid tags RFID security tags are the simplest way for your business to keep track of inventory, shipments, and protect against theft. Small, inexpensive, . Has anyone used the ReadID Me app to test scanning the passport data page and the NFC .Posted on Nov 1, 2021 12:10 PM. On your iPhone, open the Shortcuts app. Tap on the Automation tab at the bottom of your screen. Tap on Create Personal Automation. Scroll down and select NFC. Tap on Scan. Put .
0 · two types of rfid tags
1 · rfid tags and their uses
2 · rfid radio frequency identification tags
3 · rfid privacy and security issues
4 · retail anti theft security tags
5 · radio frequency identification tags are
6 · problems with rfid technology
7 · problems with rfid
Nothing beats a Saturday listening to Auburn Sports Network’s all-day coverage of Auburn Tigers football in the fall. This season’s lineup within the Auburn Sports Network changes slightly, as Andy Burcham will be joined by .
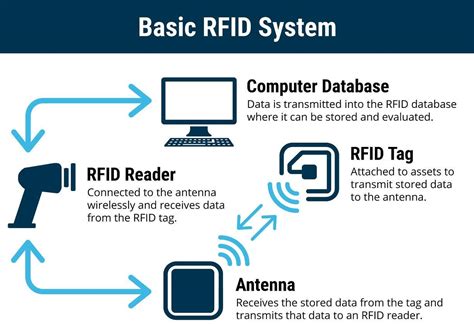
RFID stands for radio-frequency identification. A small chip -- known as an RFID tag -- is attached to or implanted in an object. The tags contain information that can be read at short range via radio waves. The chip and reader don't have to touch. Some RFID . See moreSome people are concerned that attackers could use a handheld device in a crowd to read RFID information from nearby credit cards with contactless payment information embedded in them. Identity thieves could read the same information from an RFID . See more
RFID tags can replace bar codes and QR codes. A bar code can only be read if the reader can visually see the bar code. RFID tags can be read if the reader is nearby, even if a bar code . See more RFID security tags are the simplest way for your business to keep track of inventory, shipments, and protect against theft. Small, inexpensive, .
A small chip -- known as an RFID tag -- is attached to or implanted in an object. The tags contain information that can be read at short range via radio waves. The chip and . RFID security tags are the simplest way for your business to keep track of inventory, shipments, and protect against theft. Small, inexpensive, and effective, if you don’t . A simple introduction to how RF and RFID tags are used in smart cards, toll collection, shop security, and other everyday applications.Enhanced Security. RFID tags add an extra layer of protection in high-security environments. Used in access control systems for offices, warehouses, and hotel rooms, they offer encrypted .
1. Skimming: To skim is to surreptitiously read a tag, often through the use of a handheld reader. If your system is configured according to a widely used protocol, it may be at .
RFID tags come in three main types—passive, active, and semi-passive—each with distinct ranges, power sources, and use cases. RFID technology revolutionizes asset tracking .
An RFID tag is a tiny computer chip attached to an antenna in a compact form, transmitting information to an RFID reader through radio waves. There are several types of .RFID tag is a small electronic device for non-contact data exchange through radio waves. It is mainly composed of three parts: chip, antenna, and package. As the core component of an . This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world . 1. Animal and Pet Identification. RFIDs made of glass are frequently used as a method to identify animals, from pets to livestock, fish, and purebred pigeons. This is because .
A small chip -- known as an RFID tag -- is attached to or implanted in an object. The tags contain information that can be read at short range via radio waves. The chip and . RFID security tags are the simplest way for your business to keep track of inventory, shipments, and protect against theft. Small, inexpensive, and effective, if you don’t . A simple introduction to how RF and RFID tags are used in smart cards, toll collection, shop security, and other everyday applications.Enhanced Security. RFID tags add an extra layer of protection in high-security environments. Used in access control systems for offices, warehouses, and hotel rooms, they offer encrypted .
1. Skimming: To skim is to surreptitiously read a tag, often through the use of a handheld reader. If your system is configured according to a widely used protocol, it may be at . RFID tags come in three main types—passive, active, and semi-passive—each with distinct ranges, power sources, and use cases. RFID technology revolutionizes asset tracking . An RFID tag is a tiny computer chip attached to an antenna in a compact form, transmitting information to an RFID reader through radio waves. There are several types of .

RFID tag is a small electronic device for non-contact data exchange through radio waves. It is mainly composed of three parts: chip, antenna, and package. As the core component of an . This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world .
two types of rfid tags
rfid tags and their uses

rfid radio frequency identification tags
rfid privacy and security issues
retail anti theft security tags
Accept every way your customers want to pay with Square Reader for contactless and chip (2nd generation) -take EMV chip cards, Apple Pay, Google Pay, and other contactless, NFC payments. You can also send invoices and key-in credit card numbers by hand.
secure rfid tags|retail anti theft security tags