ppt on rfid based security system This document presents a project on an RFID-based security access control system. It includes sections that describe what RFID cards are, the invention of RFID technology, different types of RFID cards, a block diagram . EDIT2: A second solution if you want to keep your card with your phone, as discovered by others. Go into settings and find "launch via NFC" in "Special app access" (you can find this by .
0 · rfid technology ppt presentation
1 · rfid technology ppt
2 · rfid tags for library books
3 · rfid system in library
4 · rfid ppt download
5 · rfid in library management system
6 · radio frequency identification ppt
7 · library automation using rfid
A subreddit for discussing credit cards. Be sure to read sub rules before posting, use the resources linked in the sidebar / about section of the sub, and use search to see if your .
This document presents a project on an RFID-based security access control system. It includes sections that describe what RFID cards are, the invention of RFID technology, different types of RFID cards, a block diagram .
The system uses an RFID reader and tags to identify authorized users and grant access by controlling a relay if their RFID code matches stored codes. An LCD displays status messages. The system provides security for .
This document presents an RFID-based access control and proximity security system project. The system uses RFID technology to track and monitor movement of people and vehicles entering and exiting educational .
Access Control, Operating System Security, and Security System Design. Outline . Access Control Concepts Matrix, ACL, Capabilities OS Mechanisms Multics Ring structure . This document presents a project on an RFID-based security access control system. It includes sections that describe what RFID cards are, the invention of RFID technology, different types of RFID cards, a block diagram of the system components, how the power supply works, descriptions of components like the LCD display and buzzer, how access is . The system uses an RFID reader and tags to identify authorized users and grant access by controlling a relay if their RFID code matches stored codes. An LCD displays status messages. The system provides security for organizations by only allowing access to people with valid RFID tags. This document presents an RFID-based access control and proximity security system project. The system uses RFID technology to track and monitor movement of people and vehicles entering and exiting educational institutions and organizations.
Access Control, Operating System Security, and Security System Design. Outline . Access Control Concepts Matrix, ACL, Capabilities OS Mechanisms Multics Ring structure Amoeba Distributed, capabilities Unix File system, Setuid Windows File system, Tokens, EFS.From Smart Homes to Smart Cities: Integrating RFID for Enhanced Security - Let's look at how RFID is helping to improve security everywhere from our homes to the bustling streets of smart cities. | PowerPoint PPT presentation | free to view
Enhanced Security: Integrating RFID and NFC with existing security systems strengthens overall security. RFID tags and NFC-enabled devices can be programmed with unique identifiers, reducing the risk of unauthorized access.This document describes an RFID-based door security system using an 8051 microcontroller and EM-18 RFID module. The system provides security to organizations by only allowing authorized personnel with valid RFID tags. Explore the history of RFID technology, its applications, and security concerns. Learn about the different classes of tags, how RFID is used in the supply chain, and the challenges of ensuring privacy. Discover the limitations of passive tags and the importance of physical barriers for privacy.
Door lock-using-rfid-technology. The document evaluates proposals from three companies for an RFID door lock system for a bank building. It analyzes the proposals based on cost, maintenance, security, and efficiency. The evaluation finds that the active RFID system best meets the criteria, being more secure and efficient while still affordable.This paper presents the design and implementation of a door locking system leveraging Radio-Frequency Identification (RFID) and fingerprint sensor technologies, orchestrated by an Arduino microcontroller. The system aims to provide robust authentication and access control, combining the convenience of RFID cards with the uniqueness of . This document presents a project on an RFID-based security access control system. It includes sections that describe what RFID cards are, the invention of RFID technology, different types of RFID cards, a block diagram of the system components, how the power supply works, descriptions of components like the LCD display and buzzer, how access is . The system uses an RFID reader and tags to identify authorized users and grant access by controlling a relay if their RFID code matches stored codes. An LCD displays status messages. The system provides security for organizations by only allowing access to people with valid RFID tags.
is the auburn game on the radio
This document presents an RFID-based access control and proximity security system project. The system uses RFID technology to track and monitor movement of people and vehicles entering and exiting educational institutions and organizations. Access Control, Operating System Security, and Security System Design. Outline . Access Control Concepts Matrix, ACL, Capabilities OS Mechanisms Multics Ring structure Amoeba Distributed, capabilities Unix File system, Setuid Windows File system, Tokens, EFS.
From Smart Homes to Smart Cities: Integrating RFID for Enhanced Security - Let's look at how RFID is helping to improve security everywhere from our homes to the bustling streets of smart cities. | PowerPoint PPT presentation | free to view
Enhanced Security: Integrating RFID and NFC with existing security systems strengthens overall security. RFID tags and NFC-enabled devices can be programmed with unique identifiers, reducing the risk of unauthorized access.
alabama auburn 2013 radio call
This document describes an RFID-based door security system using an 8051 microcontroller and EM-18 RFID module. The system provides security to organizations by only allowing authorized personnel with valid RFID tags. Explore the history of RFID technology, its applications, and security concerns. Learn about the different classes of tags, how RFID is used in the supply chain, and the challenges of ensuring privacy. Discover the limitations of passive tags and the importance of physical barriers for privacy. Door lock-using-rfid-technology. The document evaluates proposals from three companies for an RFID door lock system for a bank building. It analyzes the proposals based on cost, maintenance, security, and efficiency. The evaluation finds that the active RFID system best meets the criteria, being more secure and efficient while still affordable.
rfid technology ppt presentation
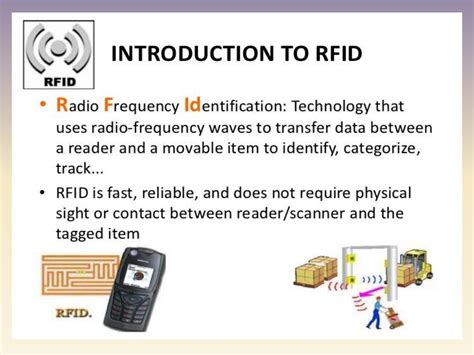
rfid technology ppt
georgia vs auburn on the radio
How to read NFC cards. The reading process is automatic and doesn’t require the user to manually configure it. To read and save the NFC card’s data, do the following: Go to Main Menu->NFC. Press Read, then hold the card near your .Android supports off-host card emulation, which means NFC card emulation with a secure element. For more information, see Host-based card emulation overview. In certain use cases such as using FeliCa for transit, off .
ppt on rfid based security system|radio frequency identification ppt